Zscaler Threat Hunting has uncovered an active espionage campaign attributed to the SideWinder APT group (also known as Rattlesnake and APT-C-17) targeting Indian enterprises through sophisticated impersonation of the nation's Income Tax Department. The campaign demonstrates evolved evasion tactics combining bureaucratic social engineering, DLL side-loading exploitation, legitimate cloud service abuse, and geofencing techniques to selectively activate malware based on victim geographic location. The operation primarily targets enterprises in Services, Retail, Telecommunications, and Healthcare sectors across India and neighboring Asia-Pacific countries.
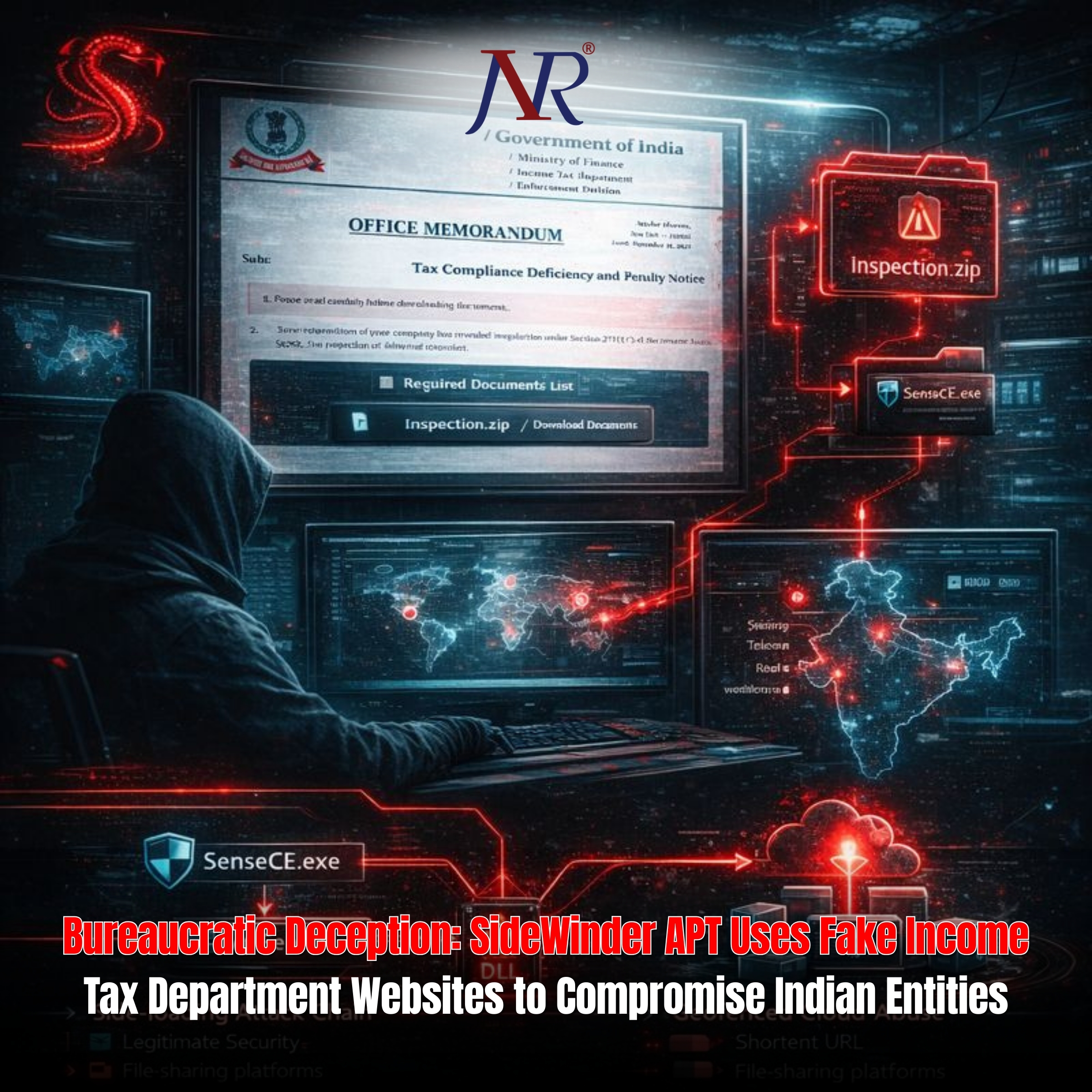
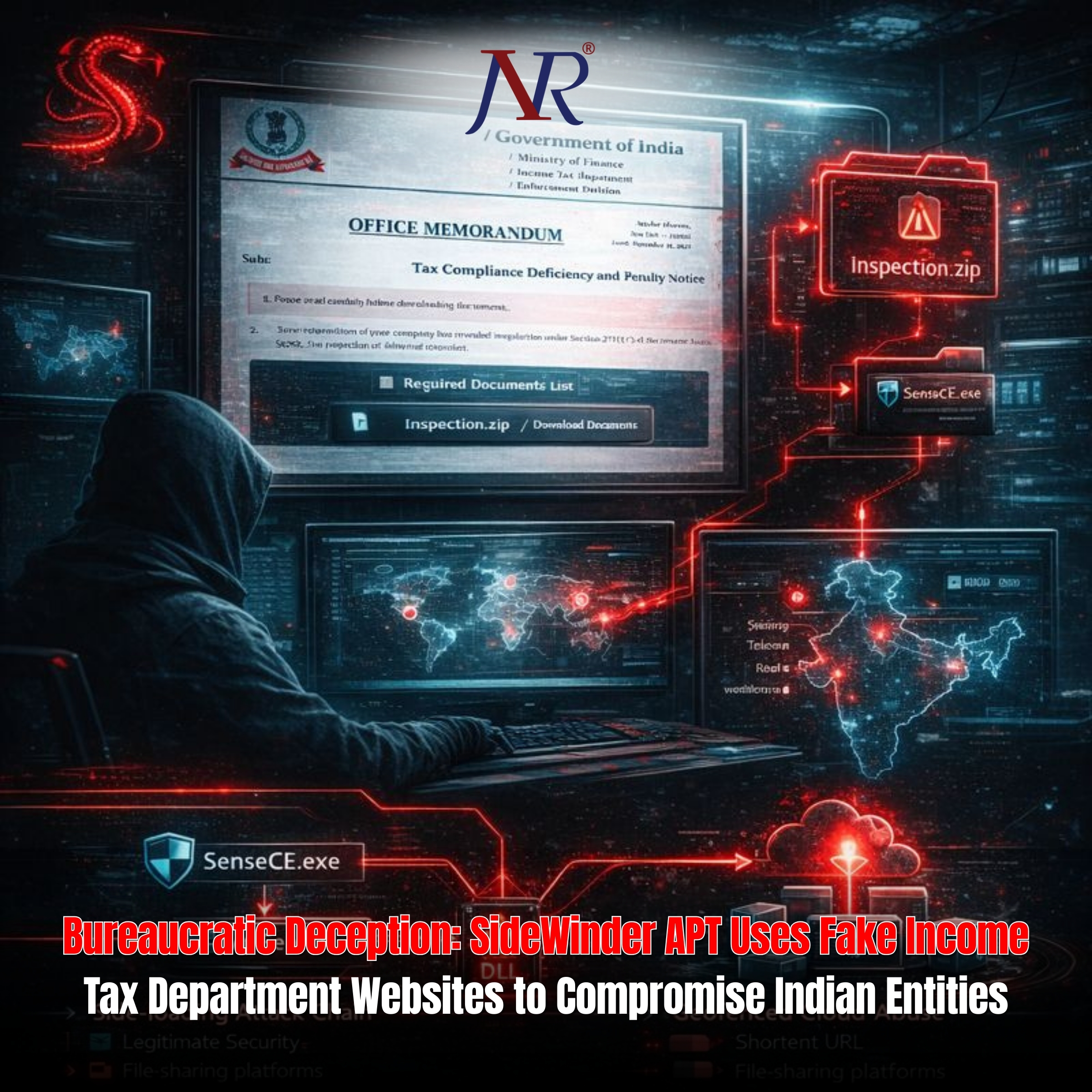
SideWinder establishes fraudulent "Income Tax Department" portals on obscure domains including gfmqvip[.]vip, designed to impersonate official government infrastructure. Phishing emails direct victims to these counterfeit portals where social engineering tactics convince users to download "Inspection.zip"—purported to be an official document review package from India's Income Tax Department.
The deception proves effective because it exploits legitimate bureaucratic processes. Indian taxpayers expect periodic compliance reviews and document inspection requests, making the phishing narrative highly credible. This contextual social engineering significantly increases victim engagement and credential harvesting success rates.
The Inspection.zip archive contains three components: a legitimate Microsoft Defender executable (SenseCE.exe), a malicious DLL (MpGear.dll), and decoy certificates designed to enhance legitimacy perception. This polyglot archive approach enables attackers to blend malicious payloads within files users perceive as official.
The attack's technical sophistication emerges through DLL side-loading exploitation. When SenseCE.exe executes, Windows' DLL search order prioritizes the malicious MpGear.dll in the same directory, causing the legitimate Microsoft Defender executable to load the attacker-controlled DLL into memory.
This technique bypasses traditional antivirus detection mechanisms because the executed binary (SenseCE.exe) appears legitimate—digitally signed by Microsoft—while the malicious DLL loads transparently within trusted process context. EDR systems often whitelist legitimate Microsoft executables, enabling the malware to execute without triggering behavioral analytics alerts.
The DLL side-loading approach represents "living off the land" exploitation, where attackers abuse legitimate system utilities to achieve execution while maintaining stealth. This technique proves particularly effective against signature-based detection and generic heuristic analysis.
SideWinder leverages trusted public services to complicate detection. URL shorteners (surl[.]li) and file-sharing platforms (GoFile.io) distribute malicious payloads through services typically classified as safe by network security infrastructure. Organizations hesitant to block legitimate platforms like GoFile.io inadvertently enable malware distribution.
Particularly sophisticated is the geofencing implementation. Victim systems contact timeapi[.]io and worldtimeapi[.]org to determine local timezone information, enabling operators to identify system location and activate malware only on devices positioned in South Asian regions. This geofencing prevents analysis by security researchers in Western regions using VPNs or analyzing captured samples outside target geography.
Once geofencing validation succeeds, victims download mysetup.exe from command-and-control servers (8[.]217[.]152[.]225 and 180[.]178[.]56[.]230). This secondary payload functions as a resident espionage implant configured to mimic Chinese enterprise software, potentially enabling attackers to maintain persistent access while remaining obscured by legitimate-appearing network behavior.
SideWinder's evolving toolkit demonstrates continuous adaptation to detection mechanisms. The group has historically maintained strong ties to Pakistan-based threat actors, with campaigns frequently targeting Indian government, military, and strategic enterprises. This Income Tax Department campaign represents geographic and sectoral expansion toward broader commercial targeting.
The campaign's success relies on credential impersonation, legitimate ecosystem abuse, technical sophistication, and targeted geofencing—a comprehensive attack synthesis requiring significant operational resources and intelligence about target behaviors.
Organizations should implement strict SSL/TLS inspection policies, block identified C2 servers, monitor suspicious execution of legitimate executables from non-standard directories, and quarantine archive files from unverified sources. Active threat hunting focused on hypothesis-driven investigation proves more effective than passive alert monitoring for detecting such sophisticated campaigns.