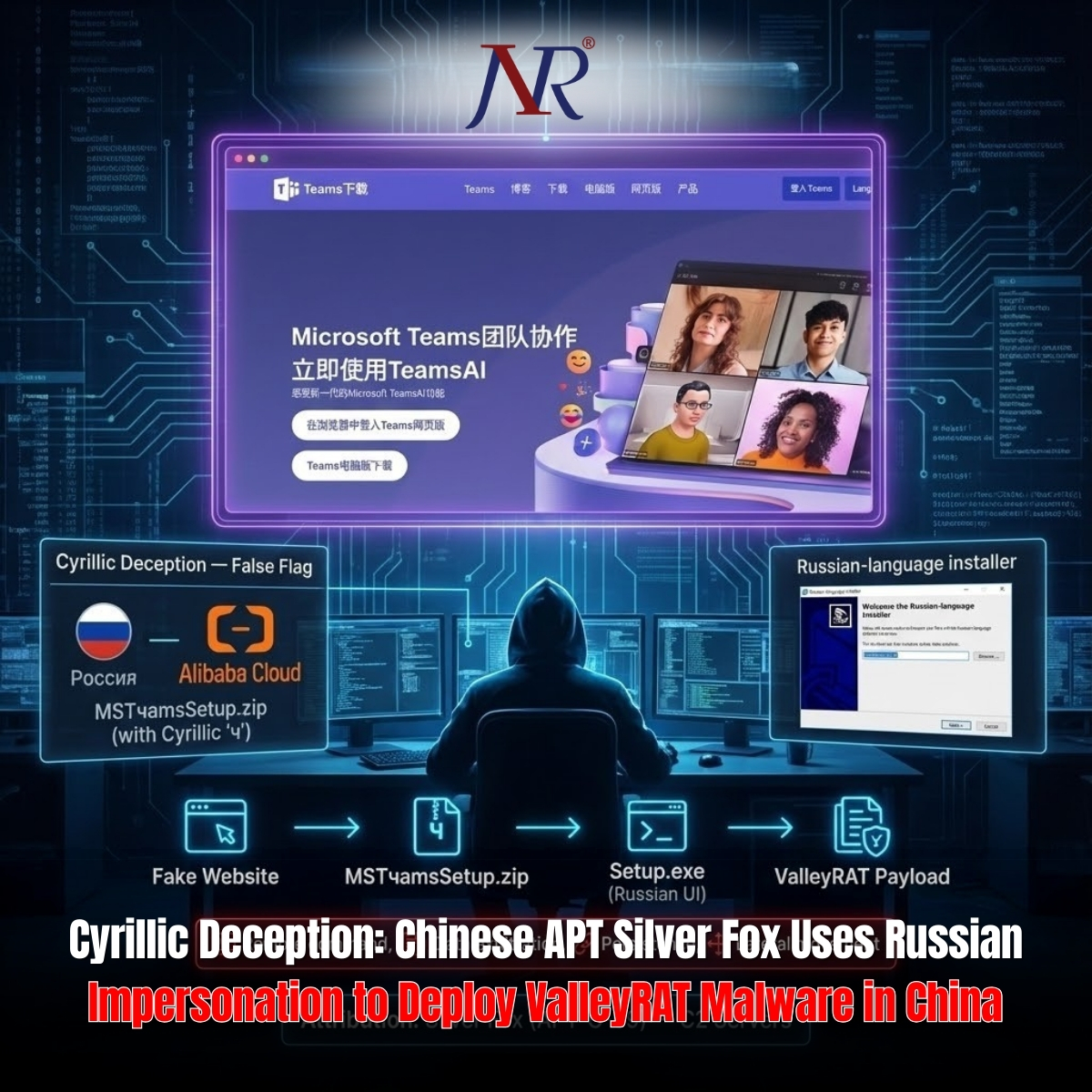
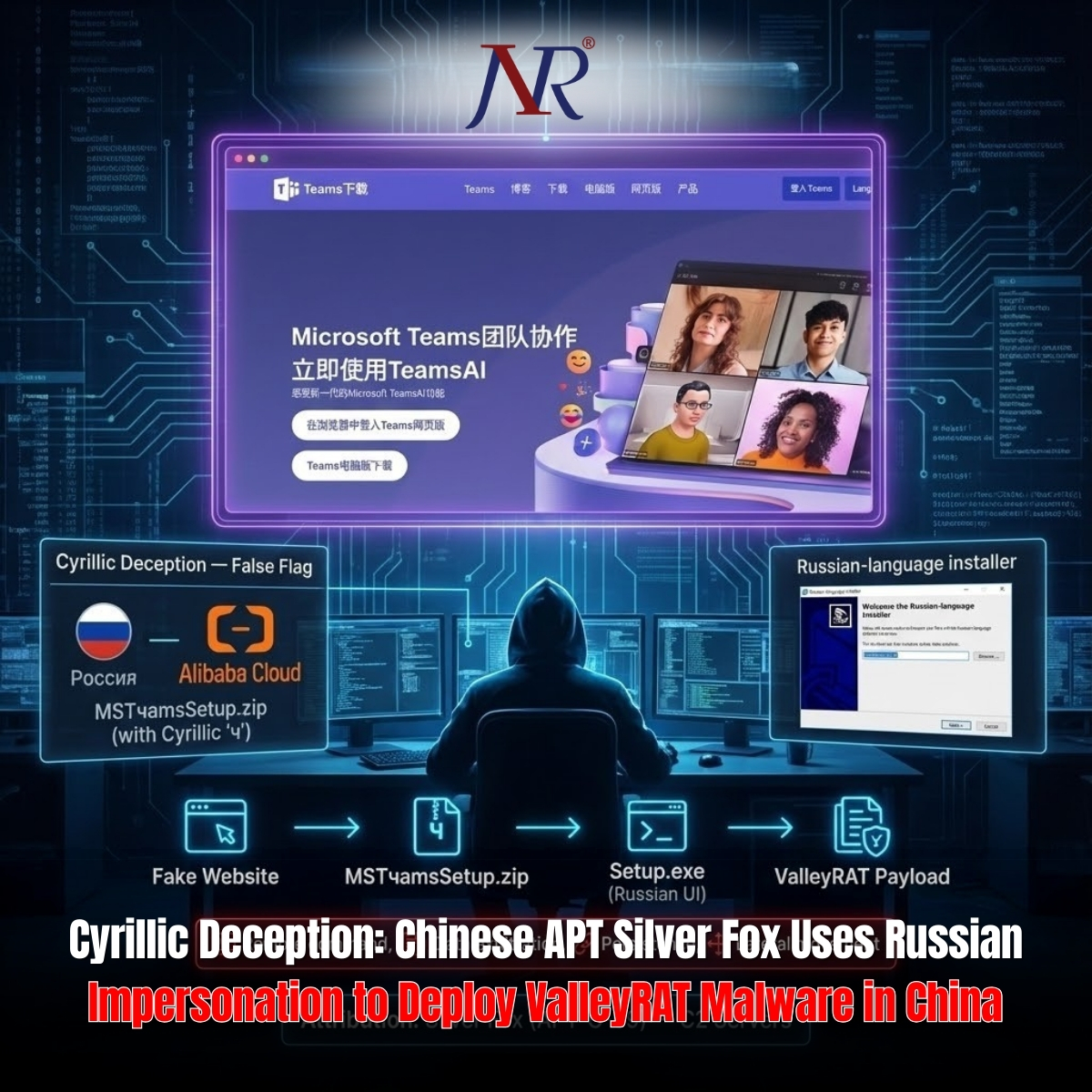
The Chinese advanced persistent threat group Silver Fox, also known as Void Arachne, has orchestrated a sophisticated false flag operation leveraging fake Microsoft Teams installers to deploy ValleyRAT malware targeting organizations operating in China since November 2025. The campaign combines search engine optimization poisoning, Cyrillic linguistic deception, and multi-stage malware execution to establish persistent remote access while deliberately impersonating Russian threat actors to mislead attribution efforts and confound incident response investigations.
ReliaQuest threat researchers have assessed with high confidence that Silver Fox deliberately embedded Cyrillic characters and Russian linguistic elements throughout the attack chain to create false attribution indicators. The malicious ZIP file itself is named "MSTчamsSetup.zip"—incorporating Cyrillic characters alongside Latin script—while the contained executable displays Russian language branding and interfaces. This deliberate deception strategy enables Silver Fox to maintain operational plausibility while misleading cybersecurity researchers and law enforcement investigating the campaign.
This attribution obfuscation aligns with Silver Fox's broader operational objectives: conducting state-sponsored espionage for sensitive intelligence collection while simultaneously engaging in financially motivated cybercrime to fund operations without requiring direct government funding. The false flag approach preserves operational security by deflecting blame toward Russian threat actors and creating ambiguity regarding genuine threat actor identification.
Silver Fox established the typo-squatting domain "teamscn[.]com," incorporating the "cn" top-level domain abbreviation specifically targeting Chinese-speaking users. The domain was initially configured in March 2025 with the HTML title "Teams downloads - Download the Microsoft Teams desktop and mobile apps" to impersonate legitimate Microsoft Teams infrastructure. In November 2025, the title was subtly modified—removing the "s" from "downloads"—to enhance authenticity and evade detection by security researchers analyzing historical domain registrations.
The SEO poisoning campaign redirects victims to the fake Microsoft Teams website where users believe they are downloading legitimate Microsoft software. Instead, a ZIP file named "MSTчamsSetup.zip" is retrieved from Alibaba Cloud storage infrastructure ("shuangkg[.]oss-cn-hongkong[.]aliyuncs[.]com"), initiating the malware infection chain. This abuse of cloud storage infrastructure adds additional obfuscation layers and complicates attribution and takedown efforts.
The trojanized "Setup.exe" executable contains sophisticated anti-analysis and evasion capabilities:
Security Tool Detection: The malware specifically searches for "360tray.exe," a component of 360 Total Security—China's dominant antivirus solution. This detection mechanism confirms Silver Fox's targeting focus on Chinese organizations and demonstrates localized threat awareness.
Antivirus Exclusion Configuration: The malware executes obfuscated PowerShell commands modifying Windows Defender exclusion lists, excluding entire drive paths (C:, D:, E:, F:) from antivirus scanning. This exclusion mechanism enables subsequent malicious components to execute without triggering antivirus detection.
Trojanized Microsoft Installer: "Verifier.exe," displayed with Russian language branding, is written to AppData\Local\ and contains modified versions of Microsoft's legitimate 32-bit C++ redistributable installer. This impersonation lowers user suspicion while enabling malware execution.
Deceptive Directory Structure: The malware writes files to directories named "Embarcadero"—mimicking legitimate integrated development environment software—and creates genuine Microsoft Teams application shortcuts. This camouflage strategy defeats visual inspection by system administrators and security personnel.
The attack proceeds through several execution stages:
File Staging: Additional malicious files are written to AppData\Roaming\Embarcadero\ directory, including "GPUCache2.xml," "GPUCache.xml," and "AutoRecoverDat.dll"—names mimicking legitimate GPU-related system files.
DLL Loading: The malware loads binary data from "Profiler.json" and "GPUCache.xml," then executes the DllRegisterServer function within "AutoRecoverDat.dll" using rundll32.exe—a legitimate Windows process. This Binary Proxy Execution technique loads the malicious DLL into trusted system process memory, bypassing detection mechanisms that lack rundll32 monitoring.
Command-and-Control Establishment: The rundll32.exe process establishes outbound connections to "Ntpckj[.]com" (IP 134.122.128[.]131) over port 18852, downloading the final ValleyRAT payload and establishing persistent remote access.
ValleyRAT—a variant of the infamous Gh0st RAT—grants attackers comprehensive system control:
Remote Command Execution: Execute arbitrary commands with compromised system privileges
Data Exfiltration: Systematically extract sensitive documents, credentials, and proprietary information
Long-Term Persistence: Establish permanent backdoor access enabling repeated unauthorized access
Lateral Movement: Compromise additional systems within organizational networks
The malware's integration with Bring Your Own Vulnerable Driver (BYOVD) techniques enables loading vulnerable kernel drivers ("NSecKrnl64.sys") to bypass security solutions and establish system-level control.
ReliaQuest's Analysis of Competing Hypotheses (ACH) methodology yielded high-confidence Silver Fox attribution through multiple evidence categories:
Shared Infrastructure: 20 related domains previously hosted fake Telegram sites in March 2025 targeting Chinese-speaking users—activity consistent with documented Silver Fox campaigns.
C2 Server Clustering: 18 additional C2 servers identified sharing identical open ports, all hosted by CTG Server LTD—a provider previously utilized by Silver Fox in historical attacks.
Malware Tooling: ValleyRAT utilization remains strongly associated with Chinese APT groups; Russian threat actors historically deploy substantially different remote access trojans.
Targeting Patterns: Campaign focus on Chinese-speaking users, specific antivirus targeting (360 Total Security), and infrastructure selection demonstrate regional specialization characteristic of Silver Fox operations.
Organizations with global operations, particularly those maintaining offices in China, should implement:
Comprehensive Logging: Enable Windows Event ID 4688 (command line events) and PowerShell Script Block Logging (Event ID 4104) to detect ValleyRAT's infection chain activities.
Employee Application Governance: Deploy self-service application catalogs providing pre-approved software for download, reducing likelihood of employees accessing malicious SEO-poisoning domains.
International Security Posture: Ensure systems in international offices—particularly China—receive equivalent security investment, logging infrastructure, and endpoint detection and response capabilities as domestic networks.
Proactive Domain and Hash Blocking: Implement automated response capabilities enabling rapid blocking of identified malicious domains and file hashes across organizational infrastructure.
The Silver Fox campaign demonstrates evolving APT sophistication: state-sponsored groups now combine traditional espionage objectives with financially motivated cybercrime operations while actively deploying false attribution strategies to complicate law enforcement and cybersecurity industry response efforts.